The Need for Full Protection, Visibility and Instant Response: Cybersecurity for Lean IT Security Teams Effective cybersecurity comes down to an organization’s ability to see and eliminate all threats....
Les mesures à prendre en cas d’attaque par ransomware Premièrement : ne paniquez pas ! Il vous faudra réagir rapidement, mais de façon méthodique. Restez calme et, le cas échéant, lancez...
Informations importantes destinées à l’utilisateur Lire ce document et les documents répertoriés dans la section sur les ressources connexes, relatifs à l’installation, la configuration et le fonctionnement de cet...
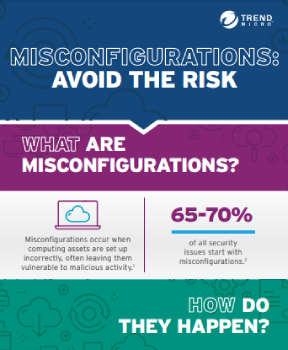
The State of Cybersecurity Lean IT security teams have plenty to be alarmed about. The most sophisticated, aggressive, and destructive cyber attacks in history have all occurred in recent...
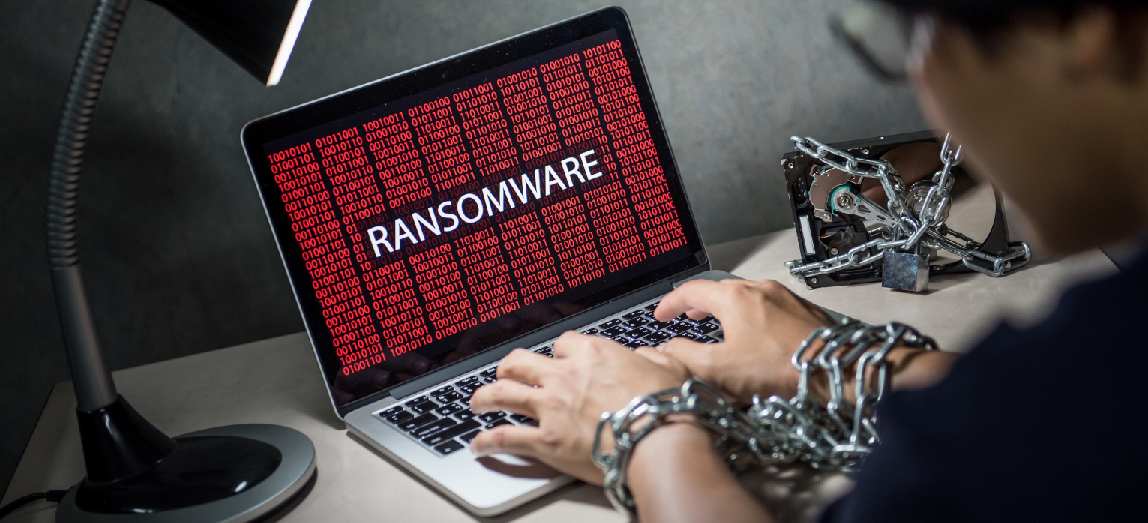
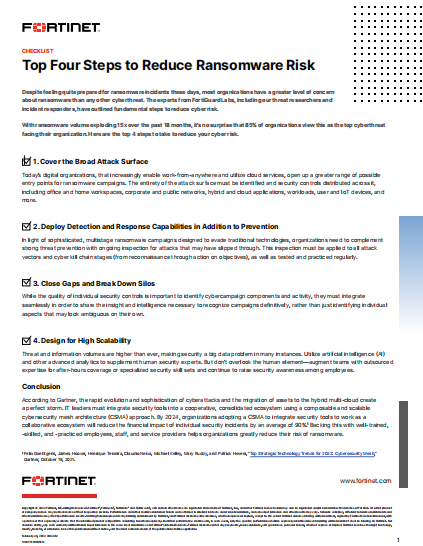
Ransomware is Here to Stay Ransomware has evolved quickly as an attack strategy. Once a hostile takeover of lone computers, today the stakes are rising. Bad actors increasingly take...
The Need for Pervasive Email Security ABSTRACT: As the number one threat vector for most organizations, email continues to be widely used by cyber criminals to penetrate organizations in...
By verifying your users’ identities before they access your network, two-factor authentication protects your applications and data against unauthorized access It works by requiring multiple factors to be confirmed before...
To be rugged is to be resilient in the face of the unexpected It’s no longer sufficient to leave security to a team of specialists who watch over the enterprise’s...
In recent years, financial and banking institutions worldwide have been the preferred targets of many cybercrime groups. Targeted attacks allow them to divert increasing sums of money, which impacts...
Sintesi preliminare Quando una minaccia informatica aumenta di 35 volte in un anno, e continua a diventare ancora più preponderante l’anno successivo, tutte le organizzazioni devono prestare attenzione. È...