Overview ESG recently completed a survey of 2,000 IT decision makers with a high level of knowledge and influence over their organizations’ end-user device environment. The survey asked respondents...
INTRODUCTION: DIGITAL TRANSFORMATION EVOLVES AND ACCELERATES The past decade has seen many big brands that we all knew and loved get smaller, shut down or get acquired, and new...
Why EDR? Companies today know that compromise is inevitable. An endpoint protection platform (EPP), such as an AV or NGAV, is the first step for stopping threats at the...
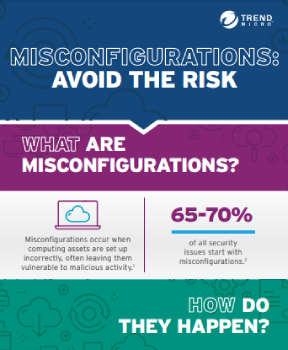
Compliance, as it relates to security protocols, is becoming crucial – if not mandatory – to maintain, yet increasingly difficult to achieve. For example, healthcare organizations must adhere to...
There has to be a better way Traditional endpoint security is a zero-sum game. The threats are constantly growing and so are the costs. Protecting endpoints is one of...
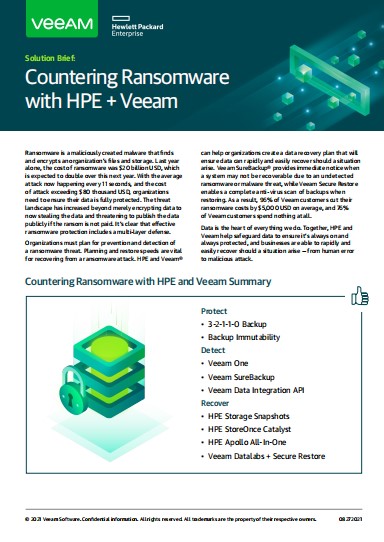
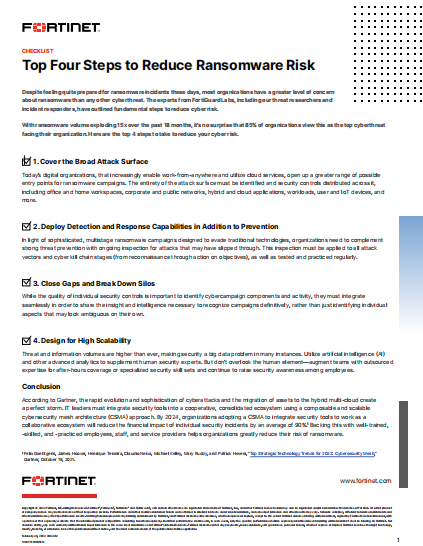
What is ransomware ? Introduction According to the National Cyber Security Center, in 2021 there was a huge increase in the amount of Protect Against Ransomware attacks reported globally....
Security orchestration, automation, and response (SOAR) is a tool category intended to maximize cybersecurity analyst efficiency by establishing workflows. Ironically, however, installing a tool authorized to take action often meets substantial...
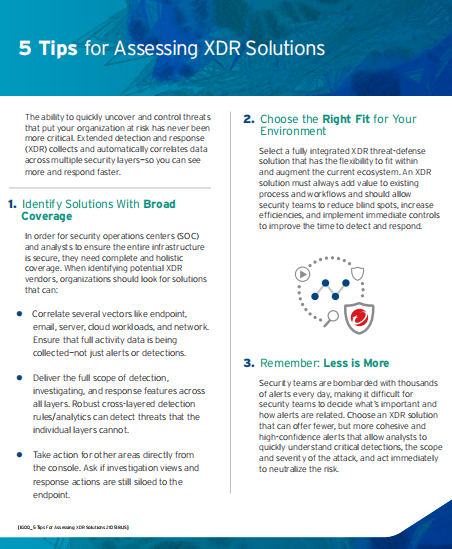
With the need for effective threat detection and response becoming more crucial by the day, cybersecurity leaders realize that partnering with a vendor is crucial. At the same time,...
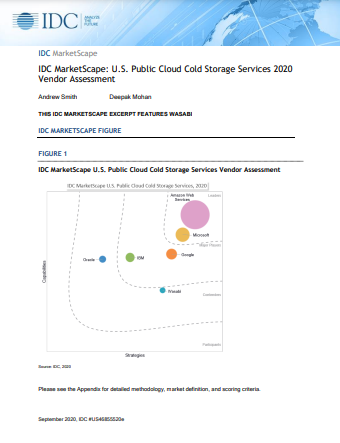
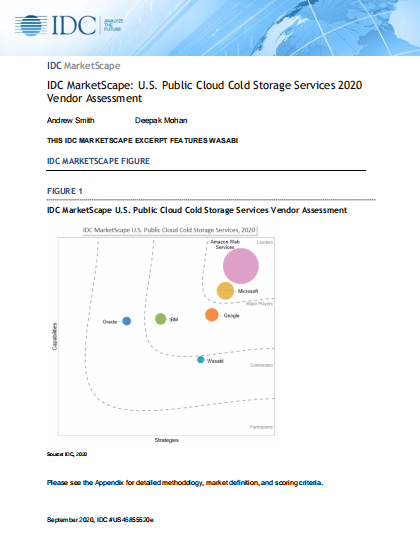
IDC OPINION Cybersecurity threats are among the highest concerns of IT managers and organizational executives alike because security incidents and data breaches can result in reputational loss, direct economic loss, and...
The Transcendence of Cloud-Native Application Development Cloud-native application development has transcended legacy infrastructure and opened doors to advanced container architecture and service platforms. With rapid integration and deployment for development...