Introduction The Pillars of Access
Computing infrastructure has a very broad meaning, but what we mean in this book is computing resources located in cloud environments, on-premise or co-located data centers, and even IoT devices on public networks. The definition of computing resources includes hardware such as servers, networking and storage, as well as infrastructure software such as databases, message queues, Kubernetes clusters, mon‐ itoring dashboards, CI/CD, and other DevOps tooling.
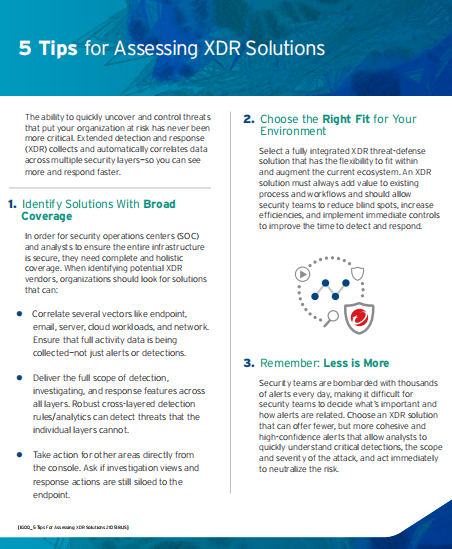
Controlling access to this complex panoply has historically relied on the notion of a network perimeter and user credentials, the digital versions of what people use to control access to their homes: a door and a set of keys. A user credential, such as a password or a private key, is nothing more than a secret piece of information that unlocks a specific perimeter. All these secrets are just data—like any data, they can be lost, shared, copied, stolen, or even sold. Neither a physical key nor a digital key guarantees the identity of someone attempting access. Simply being in possession of a secret allows to know Identity-Native Infrastructure Access Management.
Like most perimeter-based access control implementations, the front door lock on a house does nothing once an intruder gains access. Anyone with the single key to the house has access to all the valuables inside. Additional perimeter defenses inside the home have the same fundamental problem. Once an attacker is inside, everything is access Management for Infrastructure.
Corporate networks that rely on secrets and perimeter defenses have the same weak‐ ness but worse. Perimeter-based security based on secrets is inadequate because:
- The keys can be stolen, lost or have been shared with someone and duplicated later. In other words, secrets are vulnerable to human error
- As infrastructure complexity increases, there can be too many entry points to protect, increasing operational overhead
- There can be many users with different access requirements for different resources
- Once the intruder manages to gain access, they can easily pivot their attack to the adjacent resources inside the perimeter
As a company grows, a secure access model based on a perimeter and secrets does not scale.
Your computing infrastructure may consist of cloud accounts with API endpoints, VMs, databases, Kubernetes clusters, monitoring dashboards, and CI/CD tools. You may even have traditional datacenters with the same resources running in them. And every single resource requires its own access. Configuring connectivity, authen ‐ tication, authorization, and audit for every resource usually involves maintaining a myriad of configuration files, each with its own compliance requirements and syntax. As the number of resources grows, the complexity of managing access to these components becomes unsustainable—and the cost of a configuration error becomes enormous Access Management.
In this chapter, we begin the discussion of identity-based access by showing how every breach or attack relies on the very characteristics that traditional security models encourage, reviewing the pillars of infrastructure access. We will lay out the ways that true identity-based access solves all these challenges by eliminating the foundation that most infrastructure attacks rely upon: human error and the attacker’s ability to pivot.
O’Reilly offers a powerful combination of highly trusted content and unique learning experiences so you and your teams have the tools and expert guidance to work smarter and stay ahead.
To read full download the whitepaper:
Identity-Native Infrastructure Access Management