Resumen ejecutivo Cuando una ciberamenaza se multiplica por 35 en un año, y sigue siendo aún más frecuente al siguiente, toda organización debe prestar atención. Esto es exactamente lo...
The world of monitoring has fundamentally changed. Today’s monitoring tools were not designed for the complex, dynamic, and interconnected nature of cloud-native architecture. Companies need a monitoring solution that...
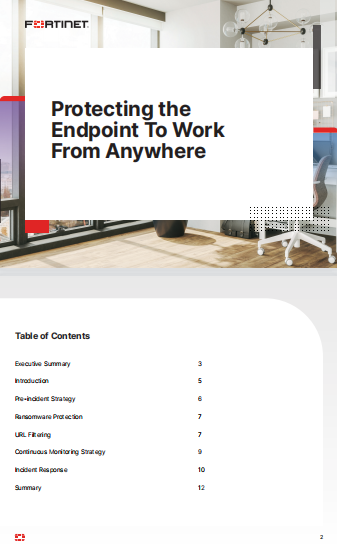
A new security strategy People work anywhere and everywhere now, from co-working spaces to coffee shops, using connected devices and cloud apps to reimagine and redefine their workdays. This...
Security & Usability for the Digital Transformation To achieve transformative business objectives, stay competitive and meet user expectations, enterprises are undergoing a digital transformation, also known as Passwordless modernization...
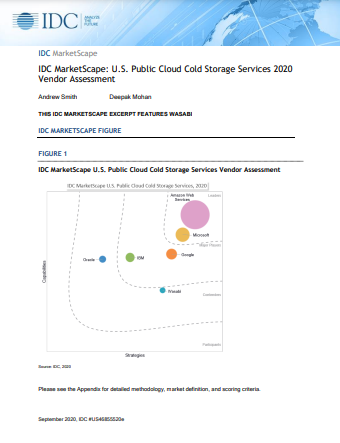
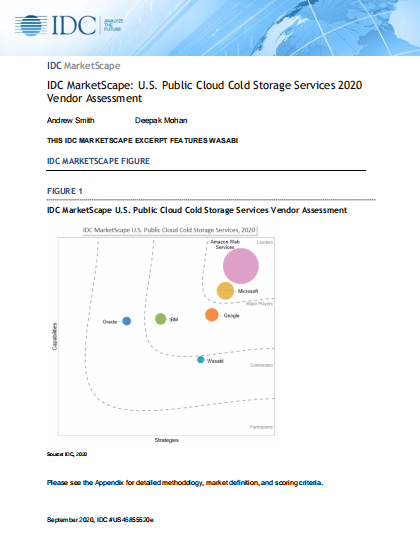
As of 2020, 91% of businesses use a public cloud and 72% use a private one. Most enterprises actually use both — with 69% opting for a hybrid solution....
À medida que as operações industriais se tornam mais conectadas, as organizações estão fazendo investimentos significativos para ajudar a proteger sua propriedade intelectual, suas operações e sua marca. Contudo,...
Digital transformation driven by the Internet of Things (IoT) is coming from seemingly everywhere within the enterprise. IT is being bombarded with requests to connect all manner of IoT...
A New Approach to Cybersecurity Traditionally, cybersecurity strategies have focused on protecting the perimeter infrastructure and layering in multiple point solutions to identify and block threats. This approach remains...
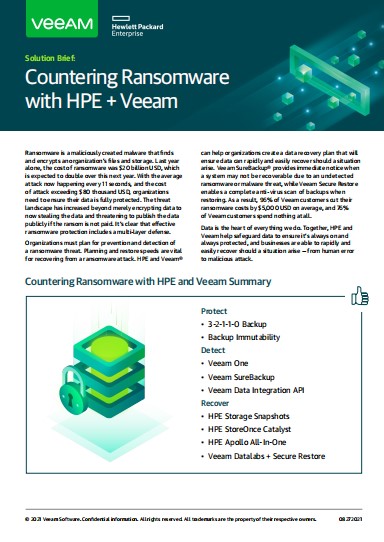
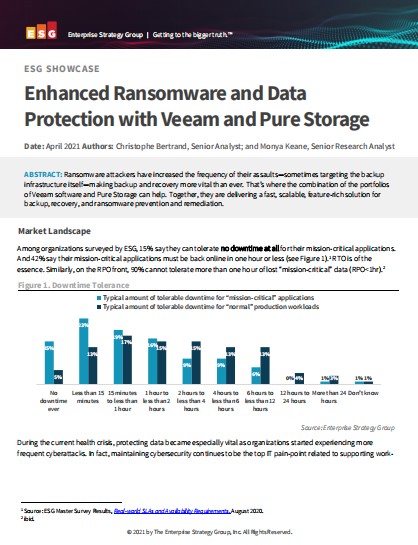
Introduction The rise of ransomware has become a crisis that has crippled organizations world-wide. New strains of ransomware and other malware threats specifically target backup data for encryption or...
Threat Detection Challenge Big data platforms such as Cloudera Data Platform can easily consume, store, manage, and analyze very large amounts of data, such as log files, application status,...