Executive Summary
Before the COVID-19 pandemic, people were already working away from the office for a variety of reasons. Back then, we had security tools like VPN to assist workers in connecting to corporate resources and other solutions like antivirus to protect the endpoint. Attackers see the growth of the hybrid work environment and the advancement of the already growing trend of employees working from home as an opportunity to exploit. They also know that corporate offices have the customer data, servers, applications, identity information, user credentials, and source code worth having. The data from June 2020 to June 2021 proves that attackers refocused on the opportunity, which explains why ransomware incidents increased nearly 1100%.1 This paper breaks apart the components that create a new environment of security complications of working from anywhere.
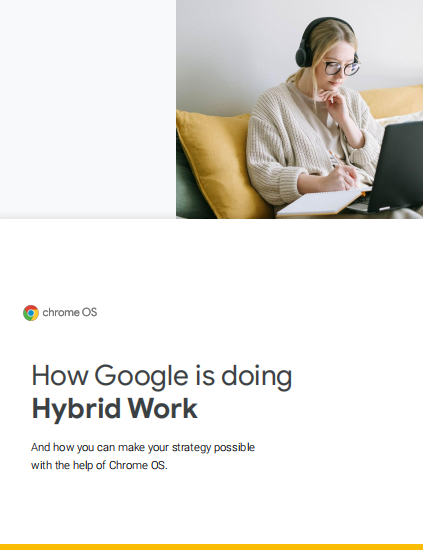
Personal Computing and Vulnerabilities
Due to supply chain issues with workstation computers as well as personal preference, the bring-your-own-device (BYOD) trend has long been an IT security threat as employees bring in previously infected devices and burden IT security teams with shadow IT. Furthermore, endpoints from any source often operate with a wide variety of critical vulnerabilities and use aging security technology that wilts in the face of an advanced attack. Organizations often don’t have visibility into roaming devices and therefore can’t calculate the risks they are shouldering.
Home Networks
Employees typically log in from a home office environment with a laptop, monitor, and external webcam. However, those home networks are often poorly secured with retail wireless routers and could contain vulnerable Internet-of-Things (IoT) devices that can act as a pathway for hackers to gain access and may already be documented on sites like Shodan. These devices can’t be managed by IT, and emails to update home routers or improve password security are ignored due to lack of initiative and technical know-how. Furthermore, the streaming of video, music, and other home internet uses takes up important bandwidth that may limit work function connectivity for things like conference calls and file sharing. In this environment, there are no extensions of corporate protections or traffic management available to save deployment time.
To read full download the whitepaper:
The Security Complications of Working From Anywhere