A growing attack surface Ransomware gangs are doubling down on attacks against multi-cloud environments. Bob Violino explores the threat and offers guidance for a more ironclad defense. The scale...
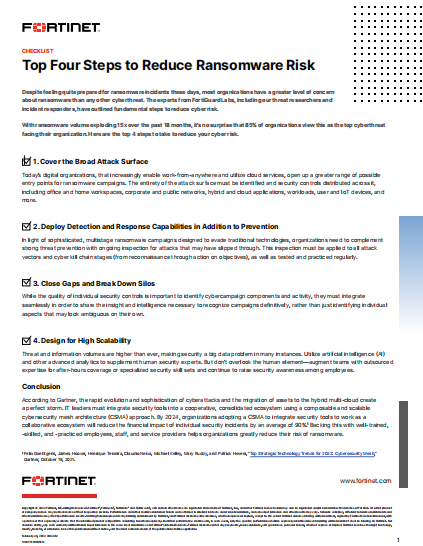
Three practical steps to protect your organisation from ransomware attacks with an identity-centric zero trust approach to security While ransomware is far from new, the rapid, global shift towards...
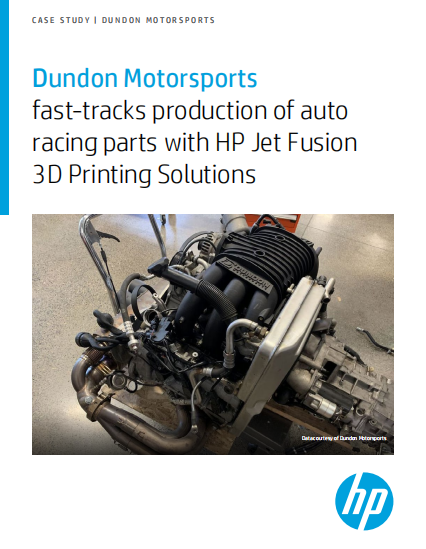
Digitize to maximize uptime As manufacturing technology advances, any innovation could be judged by one question: Does it improve uptime? Today’s era of hyperconnected manufacturing creates both new opportunities...
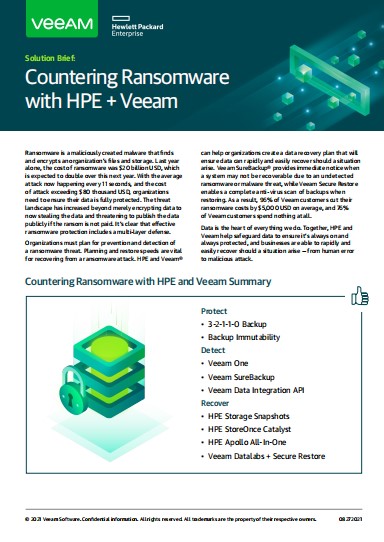
Ransomware is now one of the leading causes of data loss in the enterprise. Organizations go to great lengths to prevent ransomware attacks and to ensure data is recoverable...
What is ransomware ? Introduction According to the National Cyber Security Center, in 2021 there was a huge increase in the amount of Protect Against Ransomware attacks reported globally....
Operational Scalability When it comes to securely disposing of retired IT assets in an environmentally responsible way, scale adds complexity: the more there is, the more challenging it is...
Network and Business Leaders Must Think Differently To Build Effective Enterprise Security Hybrid IT and the adoption of work-from-anywhere WFA strategies have led to the exponential expansion of new...
Ask the Right Questions in Your Vendor Security Assessments This guide includes “must ask” questions to include in your questionnaire as part of your vendor risk management process before...
Security orchestration, automation, and response (SOAR) is a tool category intended to maximize cybersecurity analyst efficiency by establishing workflows. Ironically, however, installing a tool authorized to take action often meets substantial...
Why read this white paper? It’s an anecdote retold in a thousand and one security-conference keynote addresses and cited in a million and one articles about cybersecurity: The chief...