Threat Notification Isn’t the Solution – It’s the Starting Point Most organizations lack the in-house tools, people and processes to defend against cyber threats and manage their security program....
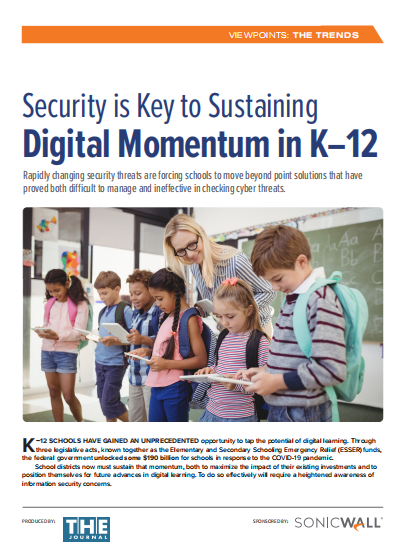
The Digital Footprint Expanded dramatically during the pandemic, with classroom deployment of 1-to-1 devices, adoption of remote teaching, the introduction of educational apps, and growing schoolwide use of Internet...
INTRODUCTION The role of the Chief Information Security Officer (CISO) has evolved significantly over the past decade as cyber threats have diversified and proliferated. With IT now integral to...
Approaching US Privacy 2023, Consumer Consent, and harnessing trust as a competitive advantage in the biopharmaceutical industry. Executive Summary And while check-box compliance is a good place to start,...
Executive Summary Phishing has long been one of the most pervasive cyberthreats, and it grows every year. According to the FBI’s Internet Crime Complaint Center (IC3), phishing reported the...
SSE. ¿Qué es y por qué debería preocuparme? El SSE es la especificación de Gartner respecto de la decisión sobre las políticas y la aplicación de estas como componentes...
SSE. O que é isso e por que devo me preocupar? O Security Service Edge (SSE) é a especificação do Gartner para funções de decisão e aplicação de políticas como componentes da estrutura Secure Access...
Meet Mary, the hybrid worker Work from Anywhere Mary is a sales representative who typically spent half of her time working on the road and half in the office....
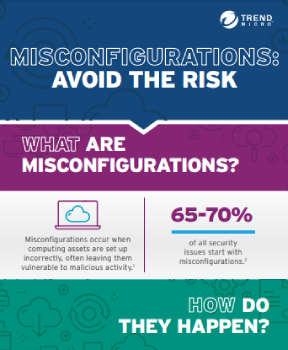
The threat landscape is always changing. Billions of ever-expanding connections are made every day by organizations across the internet. There are more things to protect than ever before. Work patterns...
Introducción El ransomware viene siendo una amenaza desde hace más de treinta años, pero recientemente la batalla ha tomado un nuevo aspecto1. En los últimos tres meses, el ransomware...