Proactive Management With Real-time Visibility Veeam’s powerful IT monitoring and analytics capabilities, powered by Veeam, provide intelligent insights and visibility that help users identify and resolve issues before they...
It pays Attackers are more motivated than ever because successful attacks offer huge payoffs. The average ransom paid by organizations in the United States, Canada, and Europe increased from...
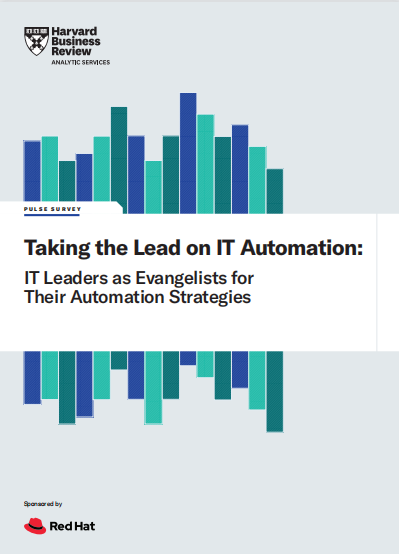
GigaOm Radar for DevOps Value Stream Management As we write this report, we are confronted with the new reality of the existential role of IT operations faced by many...
Businesses can’t prevent a cyber attack The growth and evolution of ransomware is one of the most destructive trends of the last decade. This explosion has moved ransomware from...
The Cloud Won. Now What? It is nearly impossible to think about running a business without using some cloud-based technology. From email to internal communication tools to Salesforce and...
Synthèse Lorsqu’une cybermenace se propage de façon exponentielle pendant une année et continue à prendre de l’ampleur l’année suivante, toutes les organisations doivent faire attention. C’est exactement ce qui...
Today’s Ransomware Risk Today’s ransomware is often specifically engineered to bypass traditional, prevention-oriented security controls by distributing campaigns across multiple stages, each increasingly engineered to leverage legitimate applications, communications,...
The proliferation of devices requesting access to the network, driven largely by the adoption of BYOD policies and utilization of IoT devices, has forced network security teams to be...
“Threat actors continue to pound away at organizations with a variety of new and previously seen ransomware strains, often leaving a trail of destruction in their wake.”1 The U.S....
Taking the stress out of security Maintaining strong network security has become more challenging than ever in today’s educational ecosystem. That’s because the adoption of advanced learning technologies, along...